During my own usage – for self-learning, developer group trainings and security group demonstrations I have discovered a few more vulnerabilities that I am sharing here for the benefit of those who wish to get more out of Hacme Casino.
1. Vulnerability Exploited: Insecure Direct Object Reference
For vulnerability description refer here.
As seen in the screenshot below, it is possible to download potentially any file from the web server's file system without authentication by guessing and directly referencing it's path. Here we have downloaded boot.ini which is arguably not sensitive. Nevertheless sensitive files can be potentially downloaded as well.

2. Vulnerability Exploited: Session Fixation
For information on Session Fixation refer here. Following steps confirm the vulnerability.
Step 1: Login with a fixed session ID as seen in the Paros proxy screenshot.
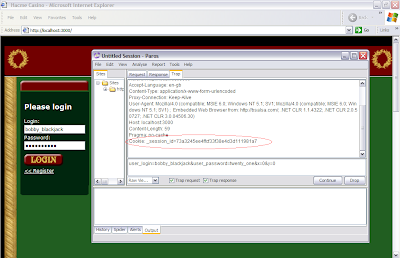 Step 2: Check the trapped response from Paros. As we see the session ID is same as what we fixed.
Step 2: Check the trapped response from Paros. As we see the session ID is same as what we fixed.
Step 3: This step is not really required but just for a double check. Let's access the OPTIONS link. The trapped session ID in Paros is definitely the one that we fixed as seen. The next screenshot confirms indeed it was possible to access OPTIONS with this session ID.


3. Vulnerability Exploited: Cross Site Request Forgery
For vulnerability description refer here. Below are additional functions that are vulnerable to CSRF. The exploitation method is same as described in Hacme Casino guide.
http://localhost:3000/account/cash_out
http://localhost:3000/account/update_options
http://localhost:3000/blackjack/bet
http://localhost:3000/video_poker/bet



Nice post
ReplyDeleteI appreciate this
Safety Is Number One Priority Buy Safety Products Online shop | Hodexo
Hodexo Digita India's
Digita India's Shooping Login It's Free And Alwyas
Digita India's Industrial
Safety Equipments
Your music is amazing. You have some very talented artists. I wish you the best of success. wettseiten paypal
ReplyDeleteThey players can see the dealer deal via web cams. The advantages of live dealer games are many. You can play games by sitting right in your room. Since the game is being viewed via webcam, you can eye everything. Casino operators
ReplyDeleteThe information you have posted is very useful. The sites you have referred was good. Thanks for sharing...
ReplyDeleteReal Money Casino Online
thanks this page and website good good The Beautiful Broken Web..
ReplyDeletePlease click on this post if you wanna paly with online casino.Thank you.
บาคาร่าออนไลน์
โกลเด้นสล็อต
I really loved reading your blog. It was very well authored and easy to understand. Unlike other blogs I have read which are really not that good.Thanks alot!
ReplyDeletereal money slots
Anonymous casino runs on Soft Swiss Casino Software, which ensures a high level of security and a powerful protection system. bitsler.com
ReplyDeleteHaving been in the casino party and planning business for many years I have heard from customers some very sad stories of what occurred at their casino fundraiser and I would like to pass to you the 7 steps you must follow to ensure you have a successful casino fundraiser and hire the BEST casino party company for your event. bandar judi online
ReplyDeleteExcellent explanation! In the online casino gambling world, people just mesmerized to play the casino games.
ReplyDelete. It was very well authored and easy to understand. Unlike other blogs I have read which are really not that good.Thanks alot! Executive Protection
ReplyDeleteI'm happy to see the considerable subtle element here!. Agen bola
ReplyDeletenice blog. Thanks for sharing.
ReplyDeleteWeb Hosting
Very helpful suggestions that help in the optimizing topic,Thanks for your sharing.
ReplyDeleteทองดีฟันขาว
While the admin of the web site is working, no question soon it will likely be famous, due to its feature blogs.
ReplyDeletehttps://magyaronlinecasino.co.hu
I am glad that I saw this post. It is informative blog for us and we need this type of blog thanks for share this blog, Keep posting such instructional blogs and I am looking forward for your future posts.แทง มวย
ReplyDeletewow ! Great blog for the playing casino.Thanks for sharing this amazing information with us, keep sharing this type of stuff.12 Play Live Casino Malaysia
ReplyDeleteThanks for sharing the info, keep up the good work going.... I really enjoyed exploring your site. good resource...
ReplyDeleteแทงบอลออนไลน์
The material and aggregation is excellent and telltale as comfortably.
ReplyDeleteWorld Emoji Day
Mesmerized article written on this blog with other relevant information. It is straight to the point that how we can improve our skills as well as how we can be represented to a new stream of professionalism.
ReplyDeletescr888 casino online
This comment has been removed by the author.
ReplyDeleteเลเซอร์หน้าใส เป็นอีกหนึ่งสิ่งใหม่ทางความงดงามที่ช่วยฟื้นฟูผิวหนังที่แห้งกระด้าง บริเวณใบหน้าหมองคล้ำให้กลับมาแจ่มใสมองเบิกบานใจ ผ่องแผ้วภายในช่วงเวลาอันเร็วทันใจ นับว่าเป็นทางลัดความงดงามที่กำลังเป็นที่นิยมสูง ช่วยดูแลผิวให้ขาวกระจ่างขาวสวยใส จากการลดลางเลือนริ้วรอยจุดด่างดำได้อย่างมีคุณภาพ
ReplyDeleteเลเซอร์หน้าใส
เลเซอร์ลดริ้วรอย
เลเซอร์รอยสิว
Thank You
ReplyDelete.............................
goldenslot
โกลเด้นสล๊อต
สล๊อตออนไลน์
goldenslot
โกลเด้นสล๊อต
สล๊อตออนไลน์
Thank You
ReplyDelete..............
goldenslot
โกลเด้นสล๊อต
สล๊อตออนไลน์
goldenslot
โกลเด้นสล๊อต
สล๊อตออนไลน์
Oh! What a brilliant job you’ve accomplished here. All the facts on this topic are available in this post. I have not read any article up till now that tells every little fact about a certain topic. I am sharing related topic which is most important for How can Diners Club Credit card numbers be generated?
ReplyDeleteWe can help inbest custom research paperswriting services. This is because of magnificent platforms of research work at our company systems are tremendous for all scholars.
ReplyDelete
ReplyDeleteI have read your article, it is very informative and helpful for me.I'm also sharing article Everything you need to know about Google Play Store.
Download Application pussy888 casino 24 HR
ReplyDeleteวิถีทางการร่วมเล่นเกมส์การพนัน pussy888ที่ง่ายอย่างยิ่งที่สุด หนทางการร่วมเล่นเกมส์การพนันที่มีเกมส์การพนันทุกแบบอย่าง เปิดให้บริการกับลูกค้าทุกคนที่เข้ามาร่วมเล่นเกมส์การพนันกับเว็บของพวกเรา pussy888 สนุกสนานกับเกมส์การพนันคาสิโน ดาวน์โหลดแอพพลิเคชั่นเกมการพนัน เล่น pussy888ได้ทุกครั้งตลอดระยะเวลา 1 วัน เว็บ pussy888ที่เปิดให้บริการกับลูกค้าทุกคนที่เข้ามาร่วมเล่นเกมส์การพนัน pussy888ที่เปิดให้บริการกับลูกค้าทุกคน ได้เข้ามาสนุกสนานกับเกมส์การพนันเว็บของพวกเราตลอดระยะเวลา 1 วัน สมัครร่วมเล่นเกมส์การพนันกับเว็บของพวกเรา เล่นเกมส์การพนัน pussy888 ทำเงินจากการเล่นเกมส์การพนันได้เลยในช่วงเวลานี้
Download Application pussy888
อัพเดทหนทางใหม่ในการร่วมเล่นเกมส์การพนันเว็บ pussy888ของพวกเรา เล่นเกมส์การพนัน pussy888ได้อย่างไม่ยากเย็น pussy888 pussy888 ร่วมเล่นเกมส์การพนันกับเว็บของพวกเรา เล่นเกมส์การพนัน pussy888ได้ทุกเวลาตลอดระยะเวลา 1 วัน เว็บ pussy888ที่เล่นแล้วได้เงินจริง เว็บ pussy888ที่พร้อมจะมอบประสบการณ์ที่เยี่ยมที่สุดเกี่ยวกับการเล่นเกมส์การพนันได้กับทุกคนที่เข้ามาร่วมเล่นเกมส์การพนัน
Download application เกมการพนันเว็บของพวกเราเดี๋ยวนี้ สำหรับเพื่อการร่วมเล่นเกมส์การพนัน pussy888 สามารถดาวน์โหลดได้อีกทั้งระบบ iOS รวมทั้ง Android Download application เกมการพนันเว็บของพวกเรา ร่วมบันเทิงใจเกมส์การพนัน pussy888 ทำเงินจากการเล่นเกมส์การพนัน pussy888ได้ไม่ยากฉะนั้น หนทางการร่วมเล่นเกมส์การพนัน pussy888ที่ง่ายอย่างยิ่งที่สุดในเวลานี้ แจ้งค่าเมลโทรศัพท์เคลื่อนที่ สามารถร่วมเล่นเกมส์การพนันกับเว็บของพวกเราได้ตลอดระยะเวลา 1 วัน เพียงแต่มีโทรศัพท์เคลื่อนที่ สามารถทำเงินจากการเล่นเกมส์การพนันกับเว็บ pussy888ของพวกเราได้ไม่ยาก
ร่วมเล่นเกมส์การพนันกับเว็บของพวกเรา สมัครเลยในเวลานี้ เล่นเกมส์การพนันกับเว็บไซต์ pussy888ที่ยอดเยี่ยม ร่วมเล่นเกมส์การพนันกับเว็บของพวกเรา ดาวน์โหลดแอปพลิเคชั่นเกมส์การพนันรวมทั้งทำเงินจากการเล่นเกมส์การพนันได้อย่างง่ายดายเว็บ pussy888ที่เยี่ยมที่สุด ที่มากับเกมส์การพนัน pussy888ทุกต้นแบบ ที่พร้อมบริการให้กับทุกคน
ร่วมเล่นเกมส์การพนันกับเว็บของพวกเรา pussy888
ด้วยเหตุผลดังกล่าวอย่าคอยช้า สำหรับใครกันแน่ที่รักในการเล่นเกมส์การพนัน pussy888 ฉะนั้นสำหรับคนไหนกันที่ต้องการจะทำเงินจากการเล่นเกมส์การพนัน ร่วมเล่นเกมส์การพนันกับเว็บของพวกเราได้เลยในช่วงเวลานี้ Download Application pussy888 เล่นเกมส์การพนันกับผู้ให้บริการเกมการพนันที่มีคุณภาพ เล่นเกมส์การพนัน pussy888ผ่านโทรศัพท์เคลื่อนที่
เพียงแต่ดาวน์โหลดแอพพลิเคชั่นเกมส์การพนัน pussy888เพียงแค่นั้น พวกเราก็จะสามารถทำเงินจากการเล่นเกมส์การพนัน pussy888ได้ แค่เพียงพวกเราดาวน์โหลดแอปพลิเคชั่นเกมส์การพนันคาสิโน พวกเราก็จะได้เล่นเกมส์การพนัน pussy888มีคุณภาพมากโดยที่พวกเราไม่มีความจำเป็นที่จะต้องเดินทางไปยังต่างชาติ ฉะนั้นร่วมเล่นเกมส์การพนันกับเว็บของพวกเรา เกม pussy888เล่นง่าย เกม pussy888ชั้น 1 ตลอดระยะเวลาที่เปิดให้บริการเกมส์การพนัน
pussy888
You posted great content As always, good updates from your blog.We gave you such a wonderful Casino service and good bonus provide all time,You play different games and win more Prizes at 918kiss Malaysia.
ReplyDeleteSports Betting Malaysia
Malaysia Slot Games
All Online Casino Malaysia
Live Casino Malaysia
Online Gambling in Malaysia
Online Casino Malaysia
Awesome article! It is in detail and well formatted that i enjoyed reading. which inturn helped me to get new information from your blog. I am sharing related topic which is mostly important for display test
ReplyDeleteThis blog is great check it out
ReplyDeleteOffice partition systems
Office meeting pods
Phone booth for sale
Soundproof phone booth
Aluminium baffle ceiling
Aluminum ceiling tile
Metal cladding systems
Glazed partition
Glass partition walls for offices
Perforated metal ceiling
Good post! We are linking to this particularly great post on our website.
ReplyDeleteBathroom Vanity With Sink
Glass Shelf For Bathroom
Heated Towel Rail
Kitchen Drawer Basket
Kitchen Wall Rack
Mirror Cabinet
Stainless Steel Mirror Cabinet
Towel Bar
Bathroom Wall Shelves
Bathroom Cabinet
Good post! We are linking to this particularly great post on our website.
ReplyDeleteMedical spa bed
Salon Table
Esthetician Bed
Electric Massage Beds
Pedicure Spa Chair
Hydraulic Massage Table
Electric Beauty Bed
Portable massage table
Medical Procedure Chair
Best massage table
Tattoo beauty chair
พีจี เกมสล็อต pg slot ธีมอาหาร น่าเล่น ให้ได้รู้จักกันได้เงินจริง 100% เล่นง่าย ได้เงินไว ต้องที่เว็บเราเท่านั้น ฝากถอนไม่มีขั้นต่ำ PG-SLOT.GAME สล็อตเว็บอันดับ 1 สมัครสมาชิกรับโบนัสทันที!
ReplyDeleteOK, that's great, thanks for this info. All the facts on this topic are available in this post. I have not read any article up till now that tells every little fact about a certain topic. visit here
ReplyDeleteI got to know about the best software secure development. Well developed blog. Visit Here
ReplyDeleteFantastic read! 🚀💬 Considering the rapid tech advancements, maybe integrating AI could add an extra layer of safeguarding? Thoughts? 🤖 #TechSecurity #pussy888 #pussy888apk
ReplyDeleteClick Now - Pussy888
Hey there! 👋 Checked out your post Ak8
ReplyDelete, and it's got me thinking about a fresh approach to security. How about incorporating gamification to make it more engaging? 🕹️🔒
Great insights on the security issues in the Hacme Casino web application! Addressing vulnerabilities like session fixation and CSRF is crucial for improving overall security.
ReplyDeleteVisit: AK8
Insightful post! Addressing security issues in applications like Hacme Casino is crucial for user safety. Thanks for sharing!
ReplyDeleteVisit: Sky777 Free Credit No Deposit
Learn data visualization and analytics with tableau course designed for beginners to advanced users.
ReplyDeleteLearn data visualization and analytics with power bi course designed to turn raw data into actionable insights.
ReplyDeleteDellbhoomi course provides dell boomi full course
ReplyDeletepractical training with real-time projects, helping learners gain industry-relevant skills and advance their IT careers confidently.
Learn Data Modeling concepts with hands-on examples, covering database design, normalization, and best practices to build efficient and scalable data systems. data modeling training
ReplyDeleteJava course offers comprehensive training from basics to advanced concepts, including OOP, collections, multithreading, and real-time application development.java online course
ReplyDelete